Most companies collect personal information, including names, addresses, and even financial data. Though this data can help companies upgrade their services, it also produces privacy risks. If companies do not protect their systems properly, hackers will steal personal data and use it for fraud or identity theft. Some companies share or sell data without asking users' consent, raising ethical issues.
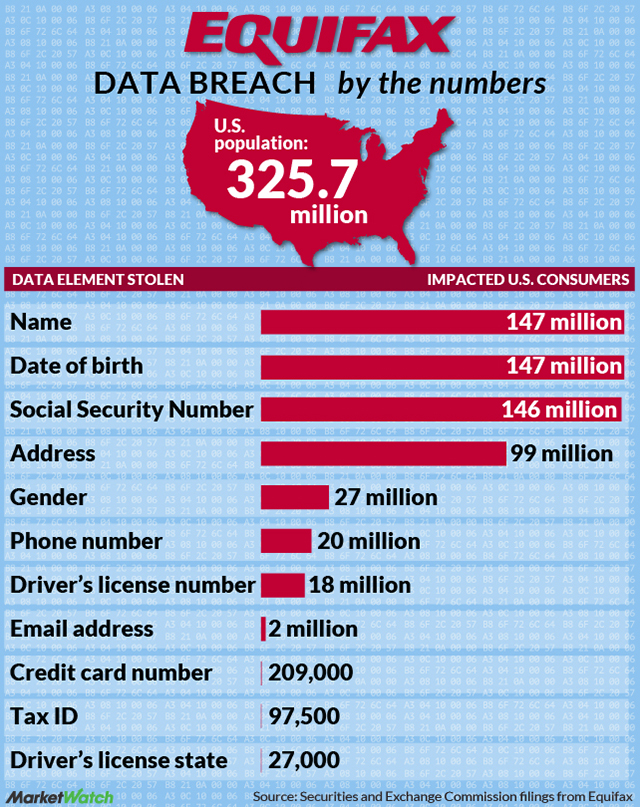
A recent example is Equifax's data breach in 2017, in which hackers stole 147 million people's personal information because of an unpatched security vulnerability. This breach gave full insight into how weak security can be and the need for companies to protect user data.
To reduce risks, companies should encrypt sensitive data, require strong passwords, and follow data protection laws like GDPR. Users can also protect themselves by being careful about the information they share online and using privacy tools like VPNs.
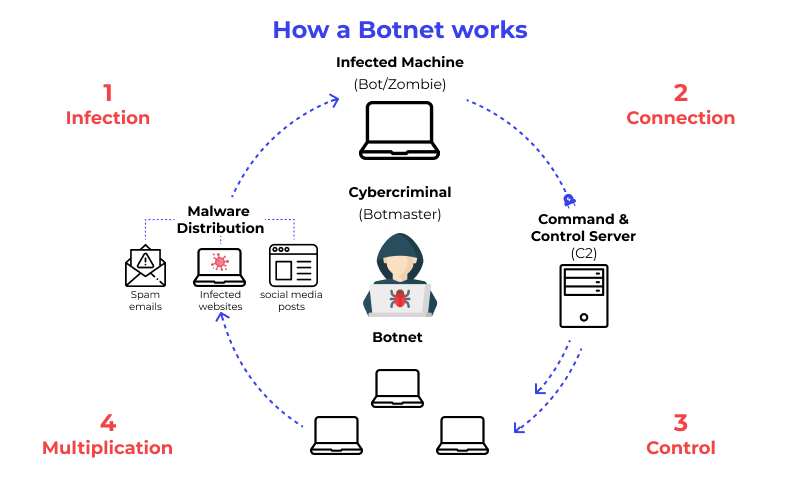
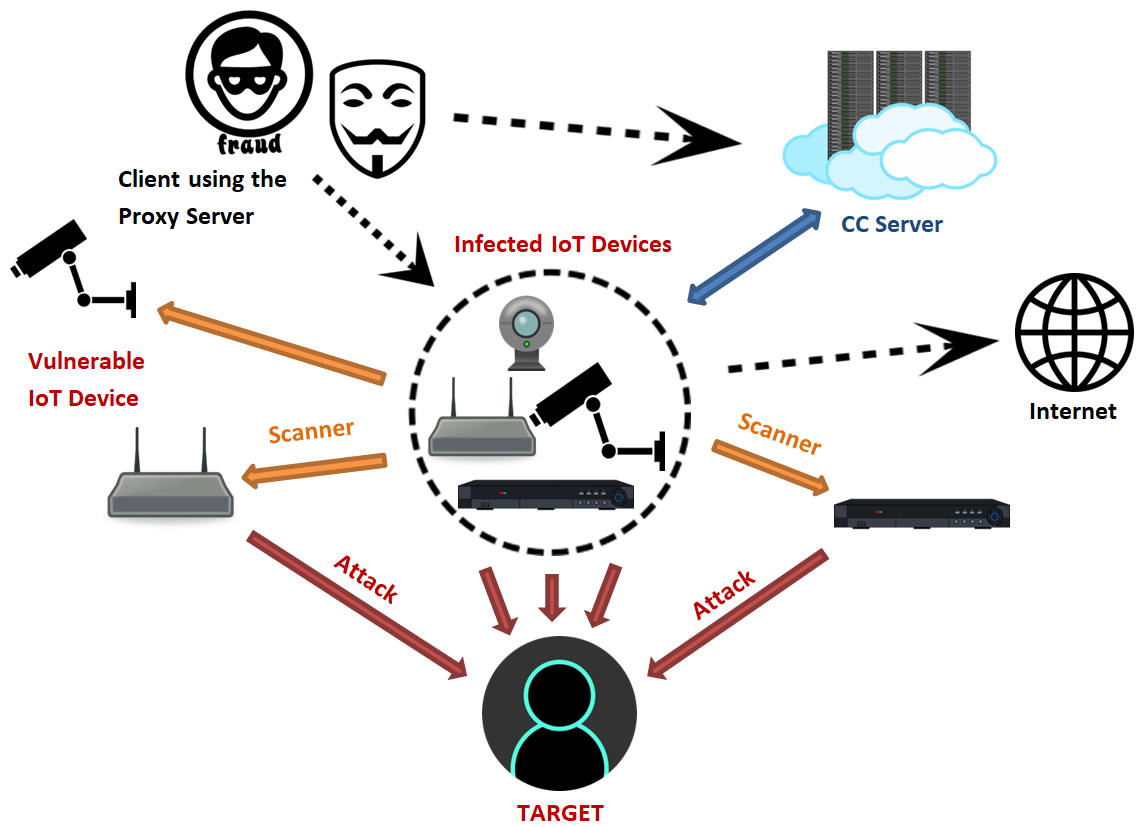
Computers, networks, and servers can be misused in different ways. An example of this is cryptojacking, which is when hackers discreetly use someone’s computer or device to mine cryptocurrency. Another example is botnets. This is when hackers hack multiple devices and remotely control them to launch cyber attacks.
One real-world example of botnets is the Mirai botnet attack in 2016. This is when hackers took control of thousands of devices and launched a cyber attack that shut down many major websites like Twitter and Netflix. This cyber attack showed how unsecured devices are used to harm the internet.
To protect computing resources, users can install strong antivirus software and update their devices. Users can also use two-factor authentication to make it harder for hackers to be able to gain access.
Case Study on Mirai Botnet Attack
Hackers and cybercriminals use different methods to break into systems and steal information. One common method is called phishing, where attackers trick people into revealing passwords by sending fake emails or messages. Other techniques include SQL injection, which allows hackers to access databases, and zero-day exploits, which take advantage of unknown security flaws.
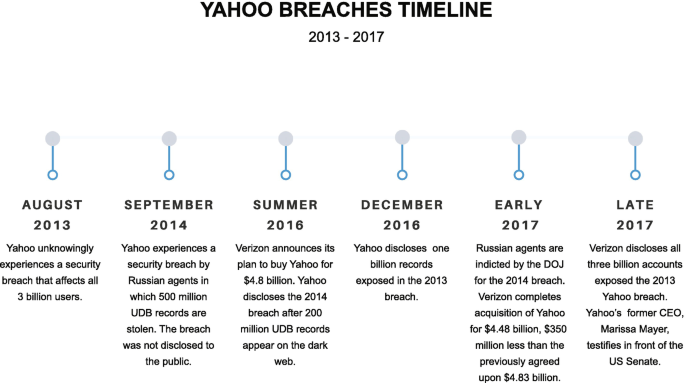
One major example is the Yahoo data breach in 2013, where hackers stole personal information from all 3 billion user accounts. This breach exposed emails, passwords, and security questions, showing how important it is to have strong security protections.
To prevent unauthorized access, people and companies should use strong passwords, enable multi-factor authentication, and be careful when clicking on links in emails. Companies should also conduct regular security tests.
Protect Yourself from Phishing
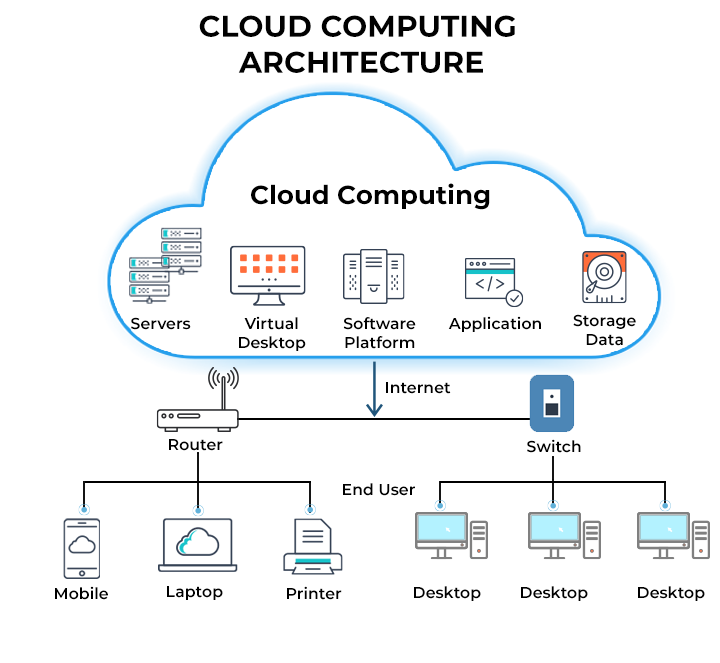
New technologies like artificial intelligence, cloud computing, and blockchain have changed the digital and physical world in many ways. They make work faster, improve communication, and increase security. However, they also come with risks, such as job loss due to AI taking over jobs and privacy concerns.
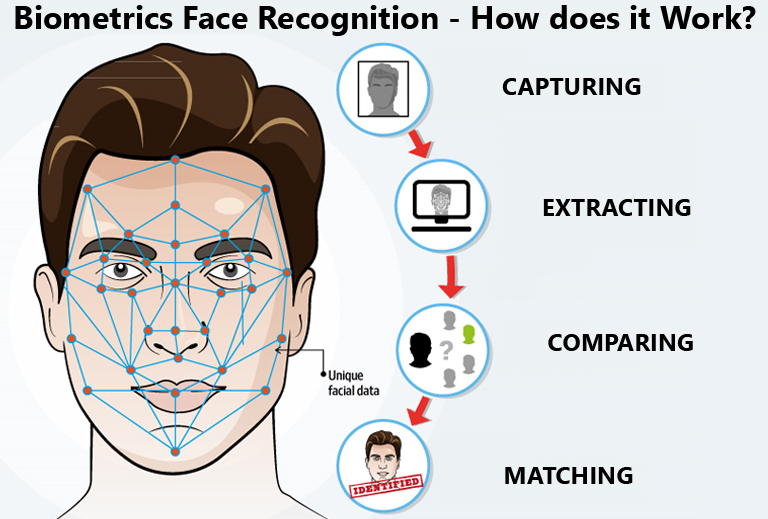
A good example is facial recognition technology. It is used for unlocking phones, security, and even finding criminals. However, it also raises privacy concerns. Some governments and companies use facial recognition to track people without their permission, which can lead to ethical problems.
To balance the benefits and risks of new technologies, companies and governments must create ethical guidelines and laws. Developers should also think about the long-term effects of their innovations to prevent harm.